Researchers of the University of Milan, Italy, have demonstrated(pdf) a Windows driver that should detect ransomware attacks and recover encrypted files. The demonstration took place during the Black Hat security conference currently held in Las Vegas.
The Windows driver is called ShieldFS and for its development the researchers identified several properties that differentiate ransomware from legitimate software. E.g ransomware scans a large number of file types and renames a lot of files. It also generates a lot of read and write actions in a short time. In order to keep track of all i/o request packets, ShieldFS uses a Windows minifilter.
By collecting this kind of data from 5 different ransomware variants in Virtual Machines, the researchers were able to train a machine learning model. They also trained the model with data from legitimate applications. That data was generated by 11 users on computers without any malware. This way they were able to store the data on the activity of more than 2,000 applications.
Besides analyzing behavior of software through a machine learning model, ShieldFS also checks for indicators of cryptographic functions in the computer's memory. The methods combined should ensure a low rate of false positives, the researchers claim.
In a test, ShieldFS was able to detect ransomware variants for which it wasn't trained, including WannaCry. This variant was detected after 133 files were encrypted by the ransomware. After detection all files could be recovered by ShieldFS as well. Recovery is possible because the system mirrors any file that is touched by an untrusted process. If ShieldFS detects that the untrusted process is ransomware, then the process is halted and files are recovered.
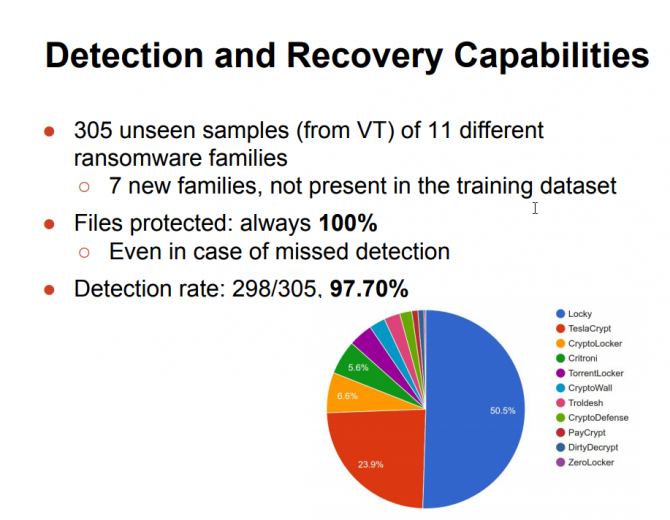
The detection ratio was about 98% in the tests and no files were lost.
The drawback of ShieldFS is that it uses system resources, like any anti-malware product. However, the researchers claim the performance on a system running ShieldFS is still acceptable for users.
ShieldFS has been developed as a 'drop-in' driver for Windows. Weak spots are ransomware variants that slowly works their way through the system or variants that create a new process for each file it encrypts. The researchers stress that ShieldFS is currently just a research project and not ready for production. Nevertheless, they filed a patent in the United States.