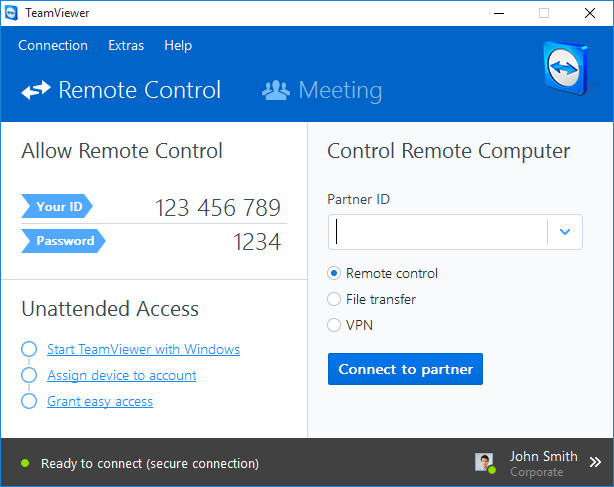
Researchers have discovered a backdoor that installs a legitimate version of TeamViewer on computers and provides attackers full access to the system this way. TeamViewer is also normally used to provide remote access to computers e.g. for remote support. Therefore the TeamViewer traffic inside a network won't stand out.
Once TeamViewer is installed attackers are able to install malware and steal data. To make sure they remain undetected the backdoor suppresses TeamViewer errors.
Researchers of Russian anti-virus vendor Doctor Web discovered an admin panel of the backdoor with IP addresses of several infected systems. The admin panel is called Spy-agent already in development since 2011. It allows cybercriminals to start and remove TeamViewer, control the webcam and microphone and download and execute files.
The majority of the infected systems was located in the United Kingdom, Spain, the United States and Russia, according to Doctor Web.