Cybercriminals target Adobe Flash Player for years already. Usually vulnerabilities in the software are exploited to install malware on the victim's computers. Sometimes malware is also disguised as a fake Flash Player update. This week, security researchers discovered an attack that combines installation of a legitimate Flash Player update with the installation of a cryptominer.
It's currently unknown where victims have downloaded the malicious combination from, according to security researcher Brad Duncan from security company Palo Alto Networks.
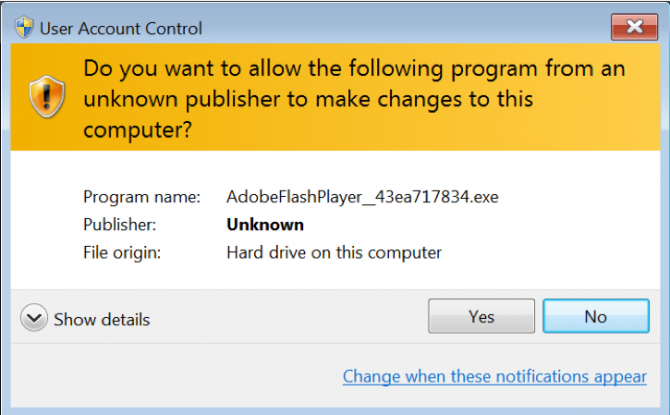
The file is offered as an Adobe Flash Player but when users execute the file, they will receive a Windows User Account Control warning that the file hasn't been properly signed. If users nevertheless decide to continue the installation, a real version of the Adobe Flash Player is downloaded. The user is also guided through the legitimate Adobe Flash Player installation wizard and a page thanking the user for installation of Flash Player on the Adobe website opens when the installation is finished. This is business as usual and the user will likely not note anything suspicious.
In the background however, also the XMrig cryptominer is installed that consumes computer resources to mine the Monero cryptocurrency.
“This campaign uses legitimate activity to hide distribution of cryptocurrency miners and other unwanted programs. Organizations with decent web filtering and educated users have a much lower risk of infection by these fake updates,” according to Duncan from Palo Alto Networks.
















