Researchers from antivirus vendor ESET, report (PDF) they have discovered the first ever UEFI rootkit that has been actively used in the wild and can survive a reinstall of the operating system and the replacement of the HDD. The rootkit has reportedly been used by a Russian hacker group.
Unified Extensible Firmware Interface (UEFI) is responsible for communication between the operating system and hardware. It's an essential part of the computer and also the first important piece of software loaded during startup. When malware is able to make changes to the firmware, it can have a large impact on the security of the system. Many attacks against UEFI have been demonstrated in the past, but until now UEFI rootkits were never found to be used in an actual attack.
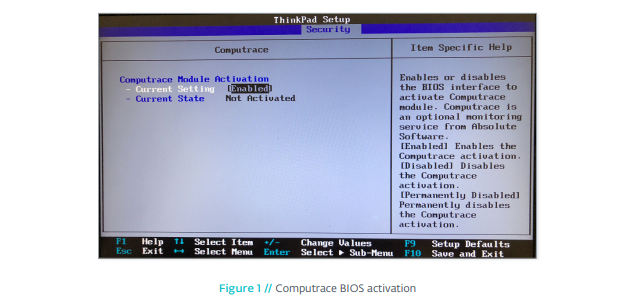
Earlier this year, security company Arbor Networks warned that attackers used anti-theft software LoJack (previously known as Computrace and can be found on e.g. Dell, HP and Lenovo laptops) to gain access to hacked machines. LoJack can be used to track stolen laptops and computers, and is embedded in the firmware of the computer. Therefore it can survive formatting or replacement of the HDD. LoJack also makes it possible to remotely execute code on the computer.
When researching systems where LoJack software was used, ESET security researchers found several tools that make it possible to read and modify the UEFI firmware. In one case the researchers found that part of the used flash memory was read, modified and written back to the chip. This way the attackers added malicious UEFI code to the flash memory. This code made it possible to execute malware during the boot process of the computer. In this case they executed malware that used the LoJack software as a backdoor.
By modifying the firmware, a rootkit can survive both the reinstallation of the operating system and also the replacement of the hard disk drive. To remove such rootkits, the UEFI firmware has to be flashed again, something the average user rarely does, according to the ESET researchers. In this case the UEFI rootkit wasn't properly digitally signed, which meant that on computers with Secure Boot (which requires all firmware components to be signed) would not be vulnerable to the attack. ESET therefore strongly recommends to enable Secure Boot on your system.
ESET suspects a Russian group related to Russian government is responsible for development of the rootkit. The group would go by names as Fancy Bear, Pawn Storm, Strontium or APT28.
















