A new type of malware first shows a fake Blue Screens of Death (BSOD), and then a fake troubleshooting wizard, to try to convince victims to buy Windows Defender Essentials, a fake non-existing version of Microsoft's Windows Defender. Fortunately there is a trick to make the malware stop doing its job.
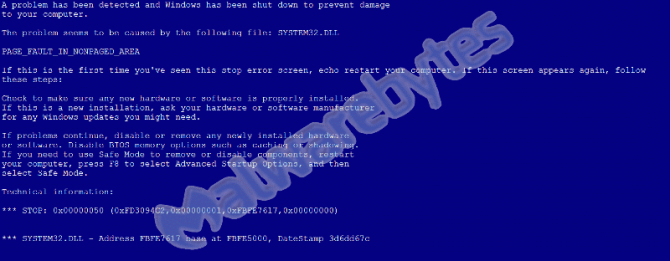
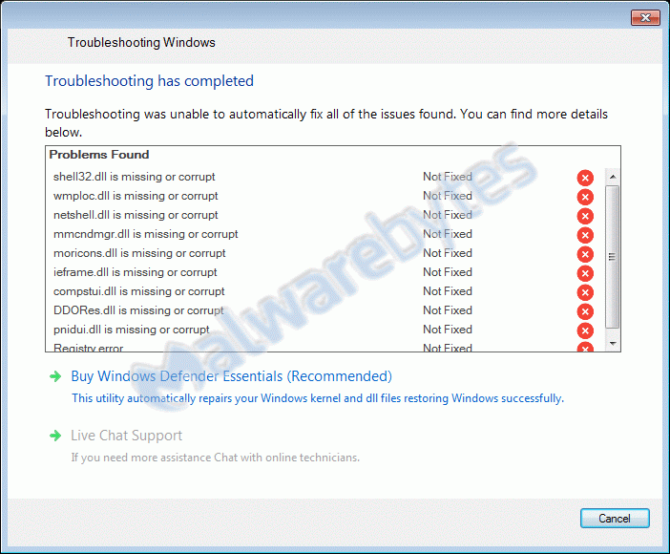
Antivirus vendor Malwarebytes reports about the malware, which goes by the name Troubleshooter, on its website. The company has posted screenshots of the entire process, that starts with a BSOD, then continues with a fake troubleshooting wizard, which in its turn detects fake issues. In the end the user is advised to purchase a fake antivirus product that should solve the issues.
The criminals behind the malware charge $25, to be paid by Paypal, for fraudulent software.
The Troubleshooter malware is distributed in various ways, Malwarebytes found their version of the malware in a cracked software installer. After the installer is executed, it loads several files that are responsible for showing the BSOD and the troubleshooting wizard. The software also makes a screenshot of the desktop and sends it to a fixed IP address, it's unknown what the reasons for that are.
One of the loaded files registers itself a a Windows Service that disables various shortcut keys. This method aims to make it for the user impossible to close the Windows with e.g. ALT + F4.
The troubleshooting wizard appears after the BSOD and also can't be closed due to the shortcut keys being disabled. Finally the wizard 'diagnoses' the issue and ends showing all kinds of corrupted files that can only be fixed with the phony Windows Defender Essential.
Users who pay $25 for the fake antivirus software, do get a fix. If they've paid they are redirected to a webpage that contains the text "thankuhitechnovation". Somehow the malware recognizes the string and terminates itself. This makes the victim believe the issue has been fixed.
Fortunately there's also a way to get rid of the malware without paying. A security researcher found that there's a built-in shortcut key that opens a windows that allows the victim to enter a website address. With CTRL+O, this window opens, the victim then has to enter the URL: "http://hitechnovation.com/thankyou.txt" which makes the malware to terminate itself, just like when one would have paid the $25.
After that, all files belonging to the malware should be removed from the computer. Malwarebytes has the removal instructions on its website.