Microsoft yesterday detected and stopped a large scale crypto-mining malware campaign. In a short amount of time, 400,000 instances of 'Smoke Loader' were detected, a trojan downloader that attempts to install malware on systems. The malware is also known as Dofoil.
In case of yesterday's attack, Smoke Loader tried to install a custom-made cryptominer that made use of NiceHash. With NiceHash it's possible to mine various cryptocurrencies. The samples that Microsoft analyzed were mining for the Electroneum cryptocurrency.
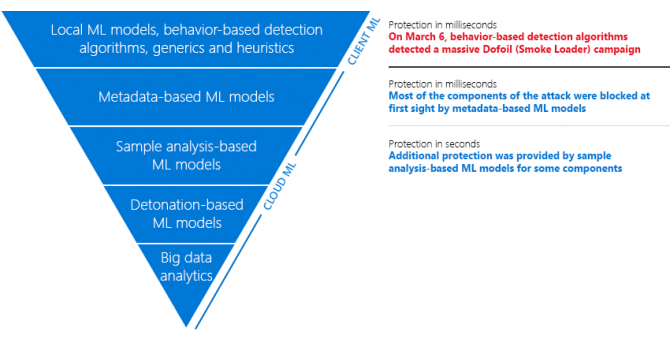
On its website, Microsoft describes how it used behavior-based detection algorithms, generics, and heuristics, as well as machine learning to detect the campaign in several minutes. In total, Microsoft detected 400,000 attempts of which 73% were in Russia, 18% were in Turkey and 4% in Ukraine.
Users on Windows 7, Windows 8.1 and Windows 10 running Windows Defender or Microsoft Security Essentials are now all protected against the malware.