A new ransomware variant is able to lock smart TVs powered by Android. The malware was discovered by the Japanese antivirus vendor Trend Micro who has called it FLocker (or Frantic Locker). 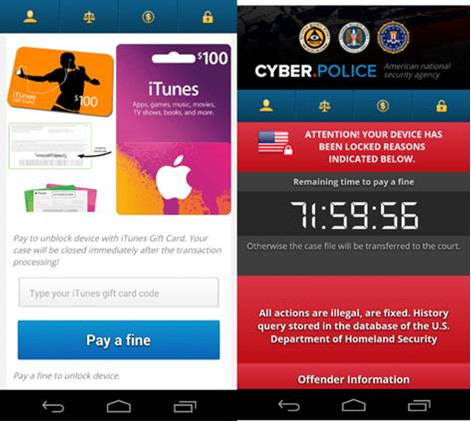
The FLocker ransomware is distributed by SMS messages and malicious links. Once the Android device is infected the ransomware locks the device and shows a message demanding a ransom. The message tries to make the victim believe that a crime has been committed. It tries to strengthen that message by displaying the name of a random law enforcement agency. The message always fits the screen, no matter if the infected system is a smartphone or smart TV.
FLocker's ransom message also shows a countdown timer that states that if the victims doesn't pay before it's down to zero the committed crime will be 'transferred to the court'.
Victims have to pay $200 in iTunes giftcards to regain access to the system.
FLocker doesn't infect Eastern European PCs
Before FLocker activates itself it first checks whether the device isn't located in Kazakhstan, Azerbaijan, Bulgaria, Georgia, Hungary, Ukraine, Russia, Armenia, or Belarus. If it is, it deactivates itself.
After the ransomware infects a system it waits for 30 minutes and then starts its locking process. During that process it shows a fake update screen. In the background the ransomware also collects data such as device information, phone number, contacts and real time location. The information is encrypted and then sent to a command and control server.
Users with an Android smart TV that are infected by FLocker should contact their TV manufacturer. It is possible to remove the malware by connecting the TV to a PC but this requires a decent level of technical knowhow.
















