The Nemucod ransomware has been found to use the free open source archive software 7-Zip to encrypt files. Nemucod is a pretty common JavaScript malware family distributed through spam emails. The malware previously only downloaded additional malware and ransomware like TeslaCrypt to PCs.
However the developer of Nemucod has added a new feature to his 'artwork', it now encrypts files itself and uses 7-Zip for the encryption routines. The Nemucod version that contains this feature is distributed by spam mails pretending to be a court appeal. When an user opens the attached JScript file the ransomware activates itself and starts to encrypt files using 7-Zip. It adds the extension .crypted to the files it successfully encrypted.
Security researcher Bart Blaze reports that it's fairly easy to stop the ransomware while it's doing its job. The ransomware starts the processes called a0.exe, a1.exe or a2.exe, cmd.exe and wscript.exe that once stopped through task manager stop further encryption of files.
In case that's not sufficient then there are encryption tools available and under development.
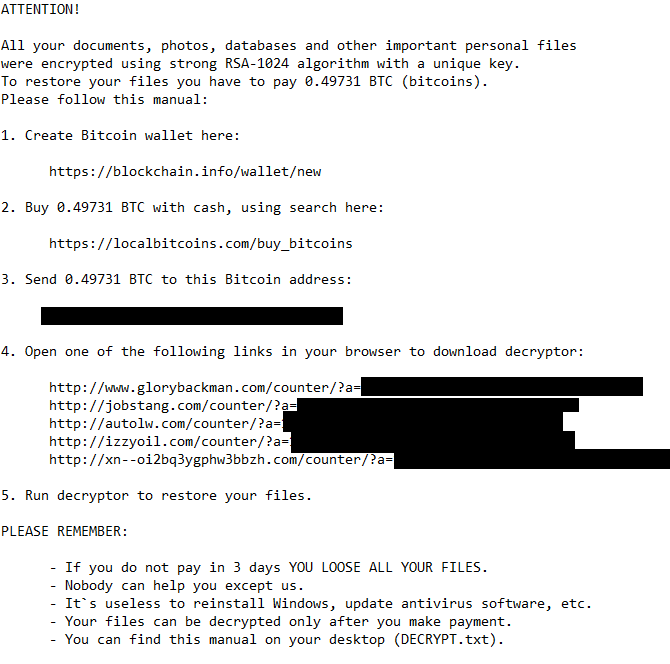
Users that were unable to stop the ransomware on time and unable to decrypt files can take the risk and pay 0.49731 Bitcoins ($220).