|
|
Review: Adata XPG SX8200 480GB NVMe SSD Reviewed by: J.Reynolds Provided by: Adata Firmware: SVN105 |
Introduction
Welcome to Myce’s review of the Adata XPG SX8200 480GB NVMe
SSD (hereafter referred to as the SX8200).
The SX8200 uses Micron’s second generation 64 layer 3D NAND
and Silicon Motion’s SM2262 Controller and Adata promises an outstanding level
of performance to satisfy the demands of the PC enthusiast.
The use of SLC caching plus a DRAM buffer does bode well so
please read on to see what we make of the SX8200.
In recent months Microsoft and Intel have acted to secure
users against the security vulnerabilities arising from the ‘Meltdown’ and
‘Spectre’ flaws. Whilst this is good news the patches do appear to have an
adverse affect upon storage performance. As part of this review we briefly
assess the impact upon my Windows 10 Desktop PC test system (please see next
page).
Packaging
To get started let’s have a look at the SX8200’s packaging -

The SX8200 is supplied with a heat spreader. In the picture
on the box cover the heat spreader has not been applied but it has been applied
to the drive sitting on the plastic container. Attaching the heat spreader is
very straight forward. Use of the heat spreader is optional, but I feel you are
well advised to use it in a desktop PC.

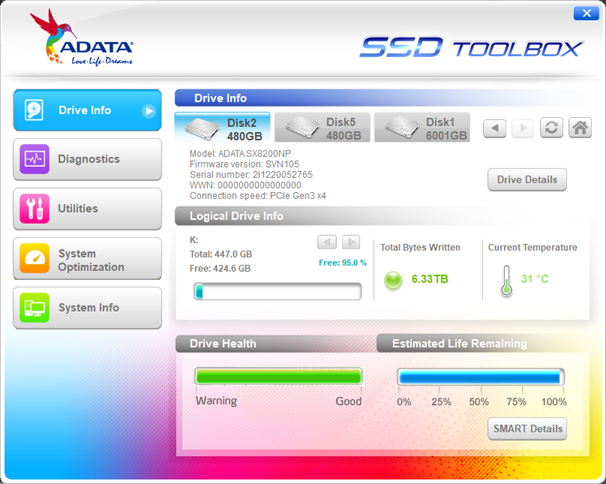
Adata provides a useful SSD utility, which can be downloaded
from Adata’s website; here is a screenshot to show the functionality it
supports –
Adata also provides a license to use Acronis True Image,
which can be used to migrate the contents of an old drive.
Market Positioning and Specification
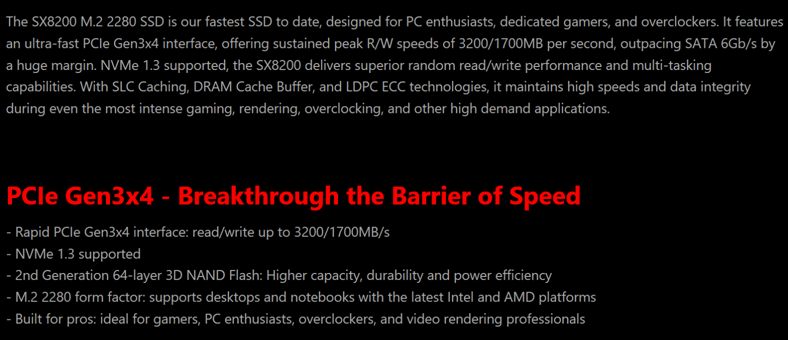
This is how Adata positions the SX8200 –
Here is Adata’s specification for the SX8200 –
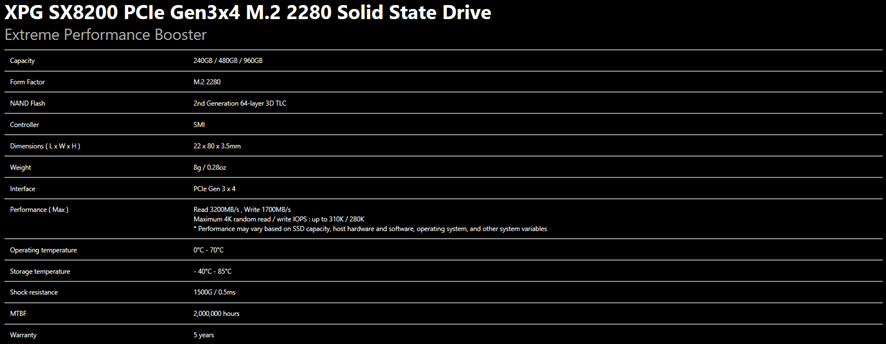
Adata does not specify an endurance level!
Now let's head to the next page, to look at the impact of
Intel’s and Microsoft’s ‘Meltdown’ and ‘Spectre’ fixes.....
NEW PAGE
NEW PAGE NEW PAGE NEW PAGE

















